使用 azd 部署 Azure 容器应用 - Openclaw Skills
作者:互联网
2026-04-17
什么是 Azure Developer CLI (azd) 容器应用部署?
Azure Developer CLI (azd) 部署技能是为寻求在 Azure Container Apps 上实现云原生应用全生命周期自动化的开发人员提供的强大解决方案。通过利用 Openclaw Skills,该工具简化了 azure.yaml 清单、Bicep 基础设施即代码模块和特定环境配置的创建。它确保涉及多个前端和后端服务的复杂部署在不同的开发环境中保持一致和可重现。
该技能强调最佳实践,如远程容器构建、托管身份和幂等基础设施更新。通过 Openclaw Skills 将其集成到您的工作流程中,可以实现本地开发与云资源之间的无缝同步,减少通常与云资源管理和服务发现相关的各种手动开销。
下载入口:https://github.com/openclaw/skills/tree/main/skills/thegovind/azd-deployment
安装与下载
1. ClawHub CLI
从源直接安装技能的最快方式。
npx clawhub@latest install azd-deployment
2. 手动安装
将技能文件夹复制到以下位置之一
全局模式~/.openclaw/skills/
工作区
/skills/ 优先级:工作区 > 本地 > 内置
3. 提示词安装
将此提示词复制到 OpenClaw 即可自动安装。
请帮我使用 Clawhub 安装 azd-deployment。如果尚未安装 Clawhub,请先安装(npm i -g clawhub)。
Azure Developer CLI (azd) 容器应用部署 应用场景
- 使用用于容器应用的声明式 Bicep 模板配置新的 Azure 基础设施。
- 自动化具有独立前端和后端 Docker 服务的多层应用程序部署。
- 使用 Openclaw Skills 管理开发、测试和生产环境的特定环境变量。
- 为 Azure 服务(如 OpenAI 和 AI Search)实施安全的基于身份的访问控制 (RBAC)。
- 使用幂等的 azd up 命令排除并修复失败的部署。
- 身份验证:使用 azd auth login 命令安全地登录到您的 Azure 订阅。
- 项目初始化:使用 azd init 构建必要的 azure.yaml 文件和基础设施文件夹结构。
- 环境设置:使用 azd env new 创建并配置独特的环境,以管理隔离的云堆栈。
- 基础设施和代码部署:运行 azd up 以配置 Bicep 资源,通过 ACR 构建容器镜像并部署服务。
- 部署后自动化:执行自定义生命周期钩子以处理 RBAC 分配、服务发现或数据库迁移。
Azure Developer CLI (azd) 容器应用部署 配置指南
要在您的项目中使用此技能,请确保已安装 Azure Developer CLI,然后执行以下命令:
azd auth login
azd init
azd env new
azd up
当使用 Openclaw Skills 更新特定服务时,可以运行:
azd deploy --service
Azure Developer CLI (azd) 容器应用部署 数据架构与分类体系
该技能通过结构化的文件和目录层级管理数据和配置:
| 组件 | 描述 |
|---|---|
| azure.yaml | 定义服务、语言和部署钩子的核心清单。 |
| infra/ | 包含用于 IaC 的 Bicep 文件 (main.bicep) 和参数 JSON 文件。 |
| .azure/ | 存储特定环境的 .env 文件和配置元数据。 |
| src/ | 存放每个应用服务的源代码和 Dockerfile。 |
| main.parameters.json | 使用 ${VAR_NAME} 语法将环境变量映射到 Bicep 参数。 |
name: azd-deployment
description: Deploy containerized applications to Azure Container Apps using Azure Developer CLI (azd). Use when setting up azd projects, writing azure.yaml configuration, creating Bicep infrastructure for Container Apps, configuring remote builds with ACR, implementing idempotent deployments, managing environment variables across local/.azure/Bicep, or troubleshooting azd up failures. Triggers on requests for azd configuration, Container Apps deployment, multi-service deployments, and infrastructure-as-code with Bicep.
Azure Developer CLI (azd) Container Apps Deployment
Deploy containerized frontend + backend applications to Azure Container Apps with remote builds, managed identity, and idempotent infrastructure.
Quick Start
# Initialize and deploy
azd auth login
azd init # Creates azure.yaml and .azure/ folder
azd env new # Create environment (dev, staging, prod)
azd up # Provision infra + build + deploy
Core File Structure
project/
├── azure.yaml # azd service definitions + hooks
├── infra/
│ ├── main.bicep # Root infrastructure module
│ ├── main.parameters.json # Parameter injection from env vars
│ └── modules/
│ ├── container-apps-environment.bicep
│ └── container-app.bicep
├── .azure/
│ ├── config.json # Default environment pointer
│ └── /
│ ├── .env # Environment-specific values (azd-managed)
│ └── config.json # Environment metadata
└── src/
├── frontend/Dockerfile
└── backend/Dockerfile
azure.yaml Configuration
Minimal Configuration
name: azd-deployment
services:
backend:
project: ./src/backend
language: python
host: containerapp
docker:
path: ./Dockerfile
remoteBuild: true
Full Configuration with Hooks
name: azd-deployment
metadata:
template: my-project@1.0.0
infra:
provider: bicep
path: ./infra
azure:
location: eastus2
services:
frontend:
project: ./src/frontend
language: ts
host: containerapp
docker:
path: ./Dockerfile
context: .
remoteBuild: true
backend:
project: ./src/backend
language: python
host: containerapp
docker:
path: ./Dockerfile
context: .
remoteBuild: true
hooks:
preprovision:
shell: sh
run: |
echo "Before provisioning..."
postprovision:
shell: sh
run: |
echo "After provisioning - set up RBAC, etc."
postdeploy:
shell: sh
run: |
echo "Frontend: ${SERVICE_FRONTEND_URI}"
echo "Backend: ${SERVICE_BACKEND_URI}"
Key azure.yaml Options
| Option | Description |
|---|---|
remoteBuild: true |
Build images in Azure Container Registry (recommended) |
context: . |
Docker build context relative to project path |
host: containerapp |
Deploy to Azure Container Apps |
infra.provider: bicep |
Use Bicep for infrastructure |
Environment Variables Flow
Three-Level Configuration
- Local
.env- For local development only .azure/- azd-managed, auto-populated from Bicep outputs/.env main.parameters.json- Maps env vars to Bicep parameters
Parameter Injection Pattern
// infra/main.parameters.json
{
"parameters": {
"environmentName": { "value": "${AZURE_ENV_NAME}" },
"location": { "value": "${AZURE_LOCATION=eastus2}" },
"azureOpenAiEndpoint": { "value": "${AZURE_OPENAI_ENDPOINT}" }
}
}
Syntax: ${VAR_NAME} or ${VAR_NAME=default_value}
Setting Environment Variables
# Set for current environment
azd env set AZURE_OPENAI_ENDPOINT "https://my-openai.openai.azure.com"
azd env set AZURE_SEARCH_ENDPOINT "https://my-search.search.windows.net"
# Set during init
azd env new prod
azd env set AZURE_OPENAI_ENDPOINT "..."
Bicep Output → Environment Variable
// In main.bicep - outputs auto-populate .azure//.env
output SERVICE_FRONTEND_URI string = frontend.outputs.uri
output SERVICE_BACKEND_URI string = backend.outputs.uri
output BACKEND_PRINCIPAL_ID string = backend.outputs.principalId
Idempotent Deployments
Why azd up is Idempotent
- Bicep is declarative - Resources reconcile to desired state
- Remote builds tag uniquely - Image tags include deployment timestamp
- ACR reuses layers - Only changed layers upload
Preserving Manual Changes
Custom domains added via Portal can be lost on redeploy. Preserve with hooks:
hooks:
preprovision:
shell: sh
run: |
# Save custom domains before provision
if az containerapp show --name "$FRONTEND_NAME" -g "$RG" &>/dev/null; then
az containerapp show --name "$FRONTEND_NAME" -g "$RG" r
--query "properties.configuration.ingress.customDomains" r
-o json > /tmp/domains.json
fi
postprovision:
shell: sh
run: |
# Verify/restore custom domains
if [ -f /tmp/domains.json ]; then
echo "Saved domains: $(cat /tmp/domains.json)"
fi
Handling Existing Resources
// Reference existing ACR (don't recreate)
resource containerRegistry 'Microsoft.ContainerRegistry/registries@2023-07-01' existing = {
name: containerRegistryName
}
// Set customDomains to null to preserve Portal-added domains
customDomains: empty(customDomainsParam) ? null : customDomainsParam
Container App Service Discovery
Internal HTTP routing between Container Apps in same environment:
// Backend reference in frontend env vars
env: [
{
name: 'BACKEND_URL'
value: 'http://ca-backend-${resourceToken}' // Internal DNS
}
]
Frontend nginx proxies to internal URL:
location /api {
proxy_pass $BACKEND_URL;
}
Managed Identity & RBAC
Enable System-Assigned Identity
resource containerApp 'Microsoft.App/containerApps@2024-03-01' = {
identity: {
type: 'SystemAssigned'
}
}
output principalId string = containerApp.identity.principalId
Post-Provision RBAC Assignment
hooks:
postprovision:
shell: sh
run: |
PRINCIPAL_ID="${BACKEND_PRINCIPAL_ID}"
# Azure OpenAI access
az role assignment create r
--assignee-object-id "$PRINCIPAL_ID" r
--assignee-principal-type ServicePrincipal r
--role "Cognitive Services OpenAI User" r
--scope "$OPENAI_RESOURCE_ID" 2>/dev/null || true
# Azure AI Search access
az role assignment create r
--assignee-object-id "$PRINCIPAL_ID" r
--role "Search Index Data Reader" r
--scope "$SEARCH_RESOURCE_ID" 2>/dev/null || true
Common Commands
# Environment management
azd env list # List environments
azd env select # Switch environment
azd env get-values # Show all env vars
azd env set KEY value # Set variable
# Deployment
azd up # Full provision + deploy
azd provision # Infrastructure only
azd deploy # Code deployment only
azd deploy --service backend # Deploy single service
# Debugging
azd show # Show project status
az containerapp logs show -n -g --follow # Stream logs
Reference Files
- Bicep patterns: See references/bicep-patterns.md for Container Apps modules
- Troubleshooting: See references/troubleshooting.md for common issues
- azure.yaml schema: See references/azure-yaml-schema.md for full options
Critical Reminders
- Always use
remoteBuild: true- Local builds fail on M1/ARM Macs deploying to AMD64 - Bicep outputs auto-populate .azure/
/.env - Don't manually edit - Use
azd env setfor secrets - Not main.parameters.json defaults - Service tags (
azd-service-name) - Required for azd to find Container Apps || truein hooks - Prevent RBAC "already exists" errors from failing deploy
相关推荐
专题
+ 收藏
+ 收藏
+ 收藏
+ 收藏
+ 收藏
+ 收藏
最新数据
相关文章
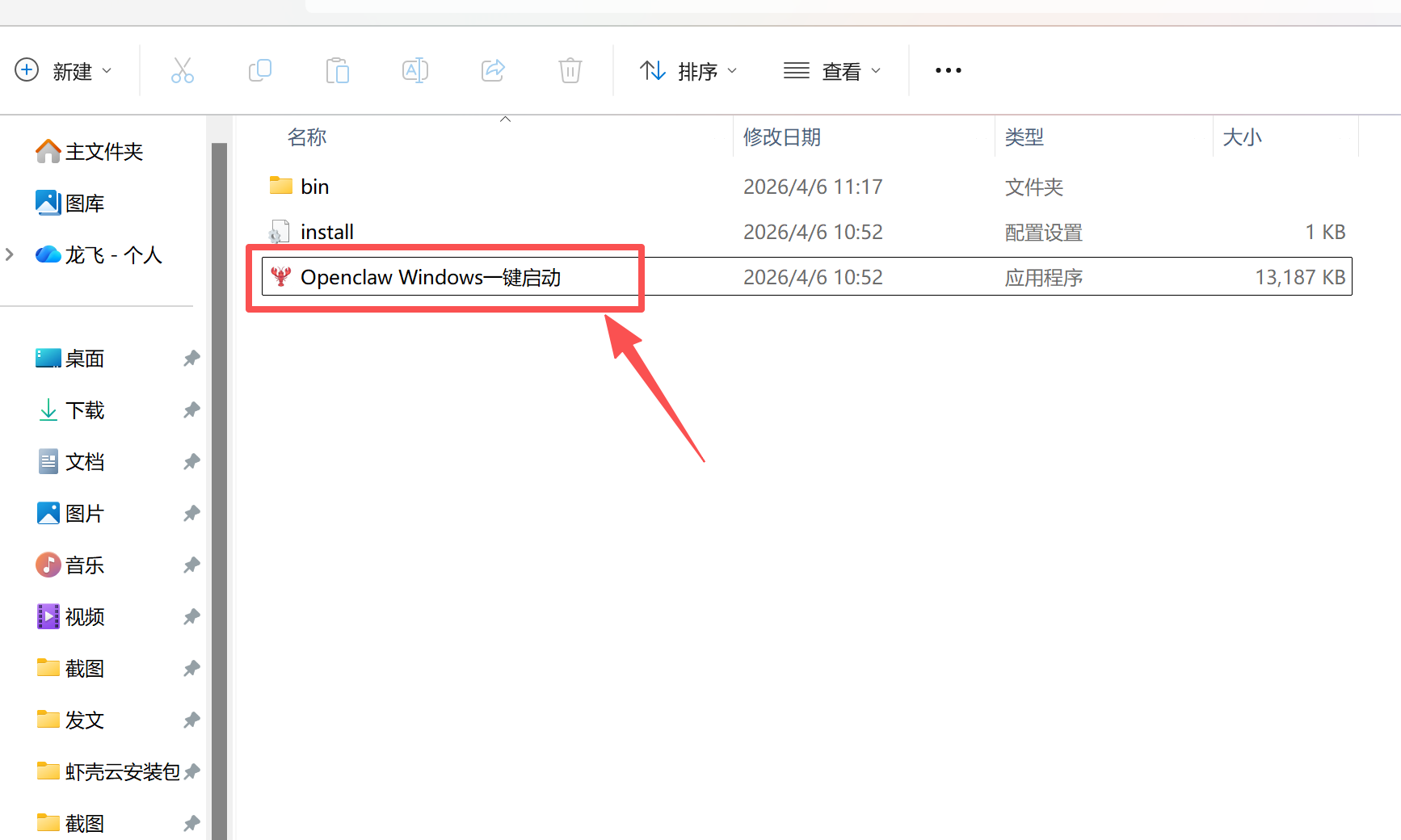
办公 AI 工具 OpenClaw 部署 Windows 系统一站式教程
Qwen3.6 正式发布!阿里云百炼同步开启“AI大模型节省计划”超值优惠
【新手零难度操作 】OpenClaw 2.6.4 安装误区规避与快速使用指南(包含最新版安装包)
OpenClaw 2.6.4 可视化部署 打造个人 AI 数字员工(包含最新版安装包)
【小白友好!】OpenClaw 2.6.4 本地 AI 智能体快速搭建教程(内有安装包)
零基础部署 OpenClaw v2.6.2,Windows 系统完整教程
【适合新手的】零基础部署 OpenClaw 自动化工具教程
开发者们的第一台自主进化的“爱马仕”来了
极简部署 OpenClaw 2.6.2 本地 AI 智能体快速启用(含最新版安装包)
代码通过即拿奖!OpenCloud 40+超热门AI工具等你来贡献
AI精选