cfshare: 通过 Cloudflare 安全共享本地端口和文件 - Openclaw Skills
作者:互联网
2026-04-18
什么是 cfshare?
cfshare 是一个专门为开发人员和 AI 代理设计的实用工具,用于为本地开发环境创建临时、安全的公共 URL。通过利用 Cloudflare Quick Tunnels,它无需 Cloudflare 账户即可绕过复杂的防火墙配置和 NAT 问题。作为 Openclaw Skills 生态系统的一部分,它为管理这些暴露提供了结构化接口,实现了对访问、生存时间 (TTL) 和内容呈现的精细控制。
无论您是需要演示在 localhost 上运行的 Web 应用,还是共享构建产物目录,cfshare 都能简化流程。它将原始 CLI 输出转化为可操作的数据,使其成为任何使用 Openclaw Skills 的自动化工作流中不可或缺的组件。该工具确保即使是复杂的网络任务也能通过简洁、可预测的 API 进行处理。
下载入口:https://github.com/openclaw/skills/tree/main/skills/ystemsrx/cfshare
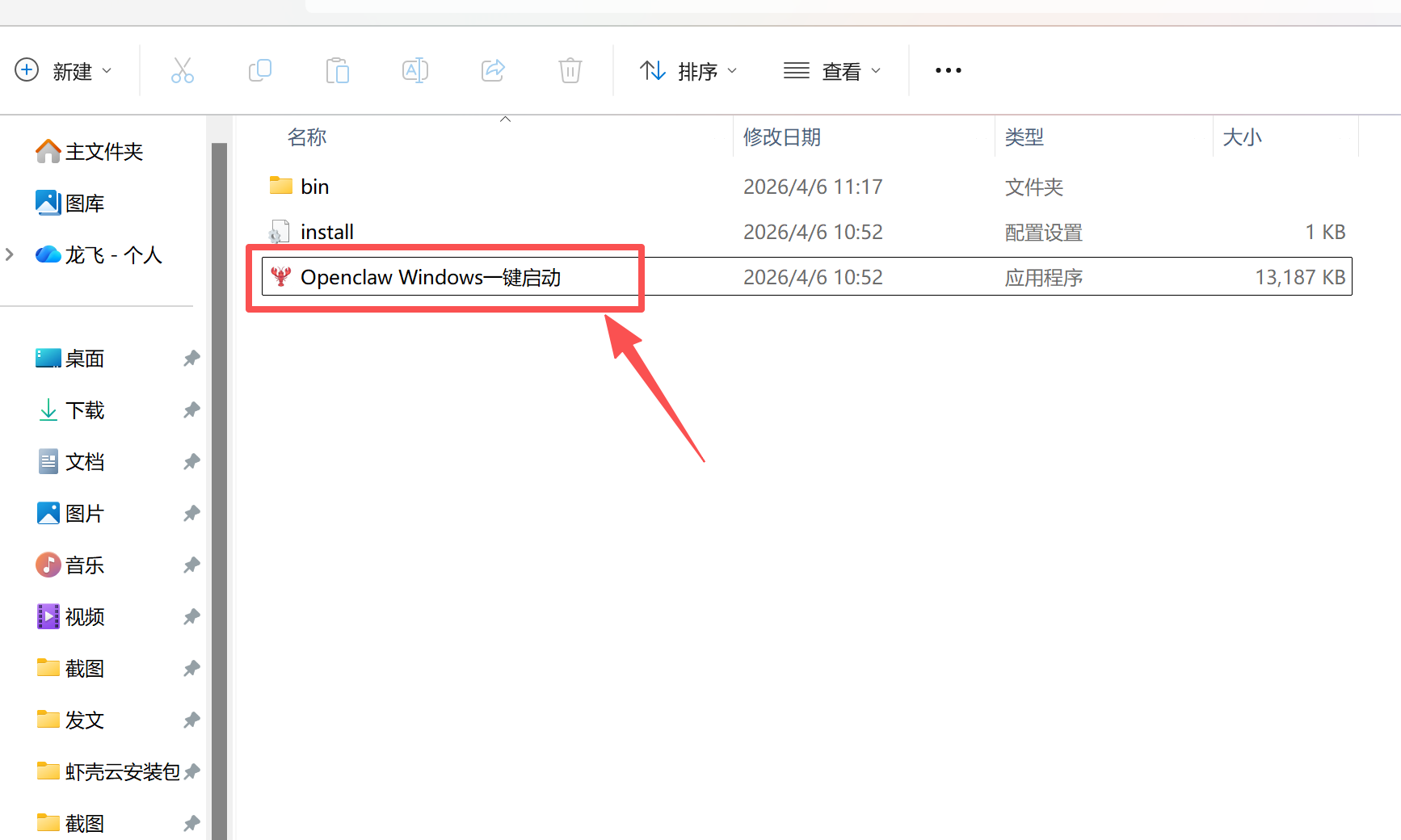
安装与下载
1. ClawHub CLI
从源直接安装技能的最快方式。
npx clawhub@latest install cfshare
2. 手动安装
将技能文件夹复制到以下位置之一
全局模式~/.openclaw/skills/
工作区
/skills/ 优先级:工作区 > 本地 > 内置
3. 提示词安装
将此提示词复制到 OpenClaw 即可自动安装。
请帮我使用 Clawhub 安装 cfshare。如果尚未安装 Clawhub,请先安装(npm i -g clawhub)。
cfshare 应用场景
- 与外部利益相关者或测试工具共享本地开发服务器(例如 React、Node.js)。
- 为本地文件或目录提供临时的公共访问权限,以便快速下载。
- 通过将本地端点暴露给公共互联网来测试 Webhook。
- 通过结构化日志和策略状态检查和审计隧道活动。
- 在浏览器环境中通过 Openclaw Skills 预览本地托管的 Markdown、图像或 PDF。
- 代理执行环境检查,以确保系统上存在必要的二进制文件。
- 用户或脚本使用 Openclaw Skills 触发针对特定本地端口或文件路径的暴露请求。
- 该技能启动 Cloudflare Quick Tunnel 并生成唯一的临时公共 URL。
- 根据提供给 CLI 合约的配置应用访问控制(如令牌或基本身份验证)。
- 会话详情(包括 URL 和过期时间戳)作为 JSON 对象返回,供立即使用。
- 可以监控、列出或手动停止会话,以清理本地工作区并关闭隧道。
cfshare 配置指南
要将其集成到您的环境中,请确保已安装所需的二进制文件。首先,检查版本:
cfshare --version
cloudflared --version
如果缺失,请通过 npm 安装 CLI:
npm install -g @ystemsrx/cfshare
然后安装 Cloudflare 守护进程(以 macOS 为例):
brew install cloudflare/cloudflare/cloudflared
此设置允许 Openclaw Skills 有效管理您的本地隧道并提供安全的外部访问。
cfshare 数据架构与分类体系
该技能在 ~/.cfshare 目录中维护状态,按如下方式组织数据:
| 文件/文件夹 | 描述 |
|---|---|
policy.json |
定义安全约束和被阻止的端口。 |
audit.jsonl |
所有暴露事件的仅追加日志,用于安全审计。 |
sessions.json |
活跃和过去隧道会话的注册表。 |
workspaces/ |
通过 expose_files 工具共享的文件的临时存储。 |
policy.ignore |
永远不应被暴露的文件模式。 |
这种结构化的方法确保了 Openclaw Skills 可以在不同会话中可靠地跟踪和管理资源。
name: cfshare description: Use the cfshare CLI to expose local ports/files as temporary Cloudflare Quick Tunnel URLs. Trigger when a user needs a temporary public URL for a local service, needs to share files/directories from terminal, or needs to inspect/export cfshare audit and policy state. metadata: { "cfshare": { "emoji": "??", "requires": { "bins": ["cfshare", "cloudflared"] }, "author": "ystemsrx" } } allowed-tools: Bash(cfshare:*)
CFShare CLI Skill
cfshare wraps Cloudflare Quick Tunnel and outputs structured JSON.
Install when version checks fail
If either command fails, install missing binaries before running any cfshare tool.
cfshare --version
cloudflared --version
- If
cfshare --versionfails, installcfshare(requires Node.js and npm):
npm install -g @ystemsrx/cfshare
- If
cloudflared --versionfails, installcloudflaredby platform:
macOS:
brew install cloudflare/cloudflare/cloudflared
Debian/Ubuntu:
curl -fsSL https://pkg.cloudflare.com/cloudflare-main.gpg | sudo tee /usr/share/keyrings/cloudflare-main.gpg >/dev/null
echo "deb [signed-by=/usr/share/keyrings/cloudflare-main.gpg] https://pkg.cloudflare.com/cloudflared $(lsb_release -cs) main" | sudo tee /etc/apt/sources.list.d/cloudflared.list
sudo apt-get update && sudo apt-get install -y cloudflared
Windows (PowerShell):
winget install --id Cloudflare.cloudflared
WSL/Linux generic binary install:
curl -fsSL https://github.com/cloudflare/cloudflared/releases/latest/download/cloudflared-linux-amd64 -o /usr/local/bin/cloudflared
sudo chmod +x /usr/local/bin/cloudflared
- Re-run both version checks. If still failing, stop and report exact stderr output to user.
CLI contract
cfshare [params-json] [options]
Supported tools:
env_checkexpose_portexpose_filesexposure_listexposure_getexposure_stopexposure_logsmaintenanceaudit_queryaudit_export
Global options:
--params 'or' --params-file--config 'or' --config-file--workspace-dir(only used byexpose_files)--keep-alive(forexpose_*, keep foreground process alive)--no-keep-alive(default forexpose_*, print result then exit)--compact
Command names accept _ and - (for example expose-port == expose_port).
Standard workflow for agents
- Run
env_checkfirst. - Create exposure with
expose_portorexpose_files. - Return
public_urlandexpires_atto user immediately. - By default,
expose_*prints result and exits. - Use
--keep-aliveonly when foreground lifecycle control is needed; stop withCtrl+Cwhen done.
Recommended for stable automation:
- Prefer
--params/--params-fileover positional raw JSON to reduce quoting errors. - Prefer
access: "token"for sensitive content. - Treat
access: "none"as publicly readable by anyone with link.
Tool usage
1) env_check
cfshare env_check
Returns:
cloudflared.ok/path/versiondefaults(effective policy + runtime paths)warnings
2) expose_port
cfshare expose_port --params '{"port":3000,"opts":{"access":"token","ttl_seconds":3600}}'
Params:
port:1..65535opts.ttl_secondsopts.access:token | basic | noneopts.protect_origin: defaultaccess != "none"opts.allowlist_paths: path prefix allowlist for reverse proxy
Returns:
idpublic_url(token mode auto-appends?token=...)local_urlexpires_ataccess_info(secrets are masked)
3) expose_files
cfshare expose_files --params '{"paths":["./dist"],"opts":{"mode":"normal","presentation":"preview","access":"none"}}'
Params:
paths: files/directories to copy into temp workspaceopts.mode:normal | zip(defaultnormal)opts.presentation:download | preview | raw(defaultdownload)opts.ttl_secondsopts.access:token | basic | noneopts.max_downloads: auto-stop after threshold
File Serving Behavior:
Mode: normal
- Single file → served directly at the root URL.
- Multiple files or a directory → displayed in an intuitive file explorer interface.
Mode: zip
- All files are packaged into a ZIP archive.
Presentation:
- Default behaviors: download | preview | raw
- Behavior can be overridden via query parameters.
- download → forces browser file save.
- preview → renders inline (images, PDF, Markdown, audio/video, HTML, text, etc.).
- raw → serves original content without any wrapper.
- If a file type is not previewable, preview automatically falls back to raw, then to download.
Returns:
id,public_url,expires_at,mode,presentationmanifest,manifest_mode,manifest_meta
4) exposure_list
cfshare exposure_list
Lists tracked sessions with id/type/status/public_url/local_url/expires_at.
5) exposure_get
cfshare exposure_get --params '{"id":"port_xxx","opts":{"probe_public":true}}'
cfshare exposure_get --params '{"filter":{"status":"running"},"fields":["id","status","public_url"]}'
Supports selector by id, ids, or filter. Can probe public reachability via opts.probe_public.
6) exposure_stop
cfshare exposure_stop --params '{"id":"all"}'
Stops tunnel/proxy/origin and removes temporary workspace. Returns {stopped, failed, cleaned}.
7) exposure_logs
cfshare exposure_logs --params '{"id":"files_xxx","opts":{"component":"all","lines":200}}'
component: tunnel | origin | all.
8) maintenance
cfshare maintenance --params '{"action":"run_gc"}'
cfshare maintenance --params '{"action":"set_policy","opts":{"policy":{"maxTtlSeconds":7200},"ignore_patterns":["*.pem",".env*"]}}'
Actions:
start_guardrun_gcset_policy(requiresopts.policyoropts.ignore_patterns)
9) audit_query
cfshare audit_query --params '{"filters":{"event":"exposure_started","limit":100}}'
10) audit_export
cfshare audit_export --params '{"range":{"from_ts":"2026-01-01T00:00:00Z","output_path":"./audit.jsonl"}}'
Runtime files (CLI mode)
Default CLI state directory is ~/.cfshare:
policy.jsonpolicy.ignoreaudit.jsonlsessions.jsonworkspaces/exports/
Important limitations in CLI mode
expose_portandexpose_filesexit by default after printing result; use--keep-aliveto hold foreground.- Current session registry is in-process memory; separate
cfshareinvocations do not restore full live session state. basicmode credentials are masked in outputs, sotokenis usually the practical authenticated mode for agent-delivered links.
Troubleshooting
cloudflared binary not found: installcloudflaredor set--config '{"cloudflaredPath":"..."}'local service is not reachable on 127.0.0.1:: start service firstpath blocked by ignore policy: adjustpolicy.ignoreormaintenance set_policyport blocked by policy: updateblockedPortsin policy if intentional
Use CFSHARE_LOG_LEVEL=info or CFSHARE_LOG_LEVEL=debug for more stderr logs.
相关推荐
专题
+ 收藏
+ 收藏
+ 收藏
+ 收藏
+ 收藏
+ 收藏
最新数据
相关文章
Minecraft 3D 建造计划生成器:AI 场景架构师 - Openclaw Skills
Scholar Search:自动化文献搜索与研究简报 - Openclaw Skills
issue-to-pr: 自动化 GitHub Issue 修复与 PR 生成 - Openclaw Skills
接班交班总结器:临床 EHR 自动化 - Openclaw Skills
Teacher AI 备课专家:K-12 自动化教案设计 - Openclaw Skills
专利权利要求映射器:生物技术与制药 IP 分析 - Openclaw Skills
生成 Tesla 车身改色膜:用于 3D 显示的 AI 图像生成 - Openclaw Skills
Taiwan MD:面向台湾的 AI 原生开放知识库 - Openclaw Skills
自学习与迭代演进:AI Agent 成长框架 - Openclaw Skills
HIPC Config Manager: 安全的 API 凭据处理器 - Openclaw Skills
AI精选