APort Agent Guardrail:Openclaw Skills 的执行前授权机制
作者:互联网
2026-04-18
什么是 APort Agent Guardrail?
APort Agent Guardrail 通过实现“先检查后行动”协议,为 AI 智能体提供了关键的安全层。它直接与框架集成以拦截工具调用(如 Shell 命令、消息传递或 Git 操作),并根据本地或托管的 Passport 策略对其进行验证。这确保了智能体在预定义的边界内运行,防止未经授权或不安全的行为。
通过在 Openclaw Skills 生态系统中使用此工具,开发者可以实现“故障关闭”的安全态势,使智能体无法绕过授权逻辑。该系统基于 Open Agent Passport (OAP) v1.0 规范构建,为各种 AI 编程环境提供了一种结构化且可审计的智能体安全方法。
下载入口:https://github.com/openclaw/skills/tree/main/skills/uchibeke/apoer-agent-guardrail
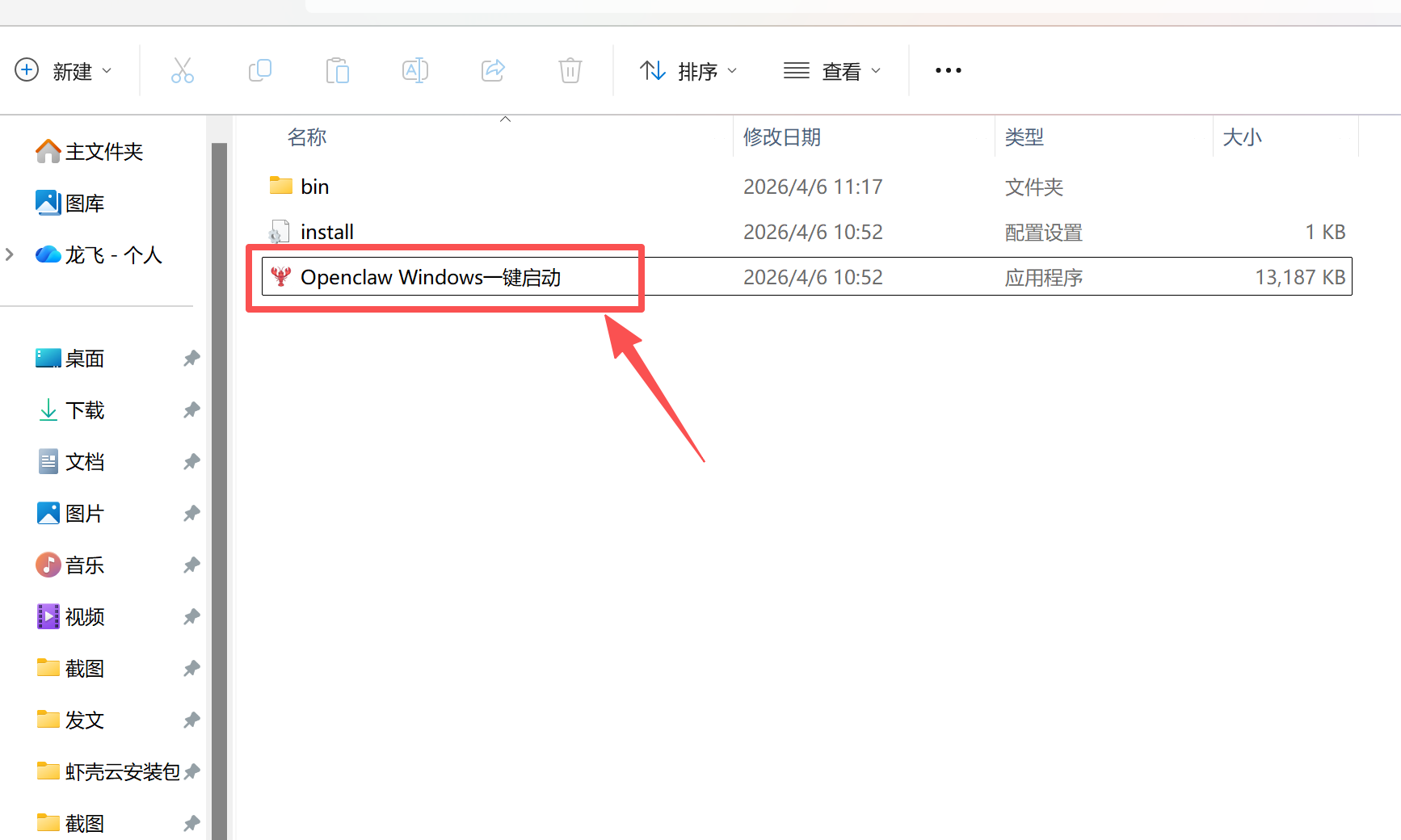
安装与下载
1. ClawHub CLI
从源直接安装技能的最快方式。
npx clawhub@latest install apoer-agent-guardrail
2. 手动安装
将技能文件夹复制到以下位置之一
全局模式~/.openclaw/skills/
工作区
/skills/ 优先级:工作区 > 本地 > 内置
3. 提示词安装
将此提示词复制到 OpenClaw 即可自动安装。
请帮我使用 Clawhub 安装 apoer-agent-guardrail。如果尚未安装 Clawhub,请先安装(npm i -g clawhub)。
APort Agent Guardrail 应用场景
- 防止自主 AI 智能体执行未经授权的 Shell 命令。
- 在自动化研究任务中限制数据导出或敏感文件访问。
- 对消息、电子邮件或社交媒体发布实施基于策略的审批。
- 通过带有签名回执和详细决策日志的记录来审计智能体操作以满足合规性。
- 在 AI 驱动的软件开发生命周期中保护 MCP 工具调用。
- AI 智能体发起工具调用,例如执行系统命令或发送消息。
- APort 插件在请求到达执行环境之前将其拦截。
- 策略引擎根据当前激活的 Passport 评估特定的工具名称及其 JSON 上下文。
- 达成确定性决策:允许 (Exit 0) 或 拒绝 (Exit 1) 该动作。
- 如果允许,工具继续执行;如果拒绝,动作将被终止,并向用户记录原因代码。
APort Agent Guardrail 配置指南
开始之前,请确保已安装 Node 18+ 和 jq。运行交互式安装程序以配置您的环境并安装必要的 Openclaw Skills 封装器:
npx @aporthq/agent-guardrails
对于使用来自 aport.io 托管 Passport 的用户,可以通过传递您的 Agent ID 来跳过向导:
npx @aporthq/agent-guardrails
安装程序会自动设置配置目录(默认为 ~/.openclaw),写入 Passport 文件,并安装所需的封装脚本。
APort Agent Guardrail 数据架构与分类体系
该技能在配置目录中组织数据,以管理策略并记录决策。所有数据均遵循 Open Agent Passport 规范。
| 文件路径 | 用途 |
|---|---|
~/.openclaw/aport/passport.json |
定义允许的工具和安全约束的核心策略文件。 |
~/.openclaw/aport/decision.json |
最近一次授权决策的日志,包括原因代码。 |
~/.openclaw/.skills/aport-guardrail.sh |
插件用于调用策略引擎的本地 Shell 封装脚本。 |
~/.openclaw/.skills/aport-guardrail-api.sh |
用于托管 Passport 配置的基于 API 的封装脚本。 |
name: aport-guardrail
description: Pre-action authorization for AI agents. Verifies permissions before every tool runs (shell, messaging, git, MCP, data export). Works with OpenClaw, IronClaw, PicoClaw. APort policy engine allows or denies each tool call deterministically; agent cannot skip it.
homepage: https://aport.io
metadata: {"openclaw":{"requires":{"bins":["jq"]}}}
APort Agent Guardrail
Pre-action authorization for AI agents: every tool call is checked before it runs. Works with OpenClaw, IronClaw, PicoClaw, and compatible frameworks. Run the installer once; the OpenClaw plugin then enforces policy on every tool call automatically. You do not run the guardrail script yourself.
Requires: Node 18+, jq. Install with
npx @aporthq/agent-guardrailsor./bin/openclawfrom the repo.
Installation
# Recommended (no clone needed)
npx @aporthq/agent-guardrails
# Hosted passport: skip the wizard by passing agent_id from aport.io
npx @aporthq/agent-guardrails
Get a Hosted Passport agent_id at aport.io after creating a passport there. OPTIONAL
From the repo (clone first): github.com/aporthq/aport-agent-guardrails — then run ./bin/openclaw or ./bin/openclaw from the repo root. Full guides: QuickStart: OpenClaw Plugin · Hosted passport setup.
You can preview your local passport at ~/.openclaw/aport/passport.json (or
The installer is interactive: it sets your config dir, passport (local or hosted), installs the APort OpenClaw plugin, writes config, and installs wrappers. After it finishes, nothing else is required—start OpenClaw (or use the running gateway); the plugin enforces before every tool call.
Wrappers (default config dir ~/.openclaw): ~/.openclaw/.skills/aport-guardrail.sh (local), ~/.openclaw/.skills/aport-guardrail-api.sh (API/hosted). The plugin uses these; you don’t call them unless testing.
Usage
Normal use: Run the installer once. After that, nothing to run manually—the plugin enforces before each tool call automatically.
Optional — direct script calls (e.g. testing or other automations):
~/.openclaw/.skills/aport-guardrail.sh system.command.execute '{"command":"ls"}'
~/.openclaw/.skills/aport-guardrail.sh messaging.message.send '{"channel":"whatsapp","to":"+15551234567"}'
- Exit 0 = ALLOW (tool may proceed)
- Exit 1 = DENY (see
/aport/decision.json /decision.json
For API mode / hosted passports:
APORT_API_URL=https://api.aport.io ~/.openclaw/.skills/aport-guardrail-api.sh system.command.execute '{"command":"ls"}'
Tool name mapping
| When you're about to… | Use tool_name |
|---|---|
| Run shell commands | system.command.execute |
| Send WhatsApp/email/etc. | messaging.message.send |
| Create/merge PRs | git.create_pr, git.merge |
| Call MCP tools | mcp.tool.execute |
| Export data / files | data.export |
Context must be valid JSON, e.g. '{"command":"ls"}' or '{"channel":"whatsapp","to":"+1..."}'.
Why this skill?
- Deterministic – runs in
before_tool_call; the agent cannot skip it. - Structured policy – backed by Open Agent Passport (OAP) v1.0 and policy packs.
- Fail-closed – if the guardrail errors, the tool is blocked.
- Audit-ready – decisions are logged (local JSON or APort API for signed receipts).
Pair it with other threat-detection tooling if needed; enforce policy through this guardrail so unsafe actions never run.
Docs
This repo: QuickStart: OpenClaw Plugin · Hosted passport · Tool / policy mapping
OpenClaw: CLI: skills · Skills · Skills config · ClawHub
相关推荐
专题
+ 收藏
+ 收藏
+ 收藏
+ 收藏
+ 收藏
+ 收藏
最新数据
相关文章
Minecraft 3D 建造计划生成器:AI 场景架构师 - Openclaw Skills
Scholar Search:自动化文献搜索与研究简报 - Openclaw Skills
issue-to-pr: 自动化 GitHub Issue 修复与 PR 生成 - Openclaw Skills
接班交班总结器:临床 EHR 自动化 - Openclaw Skills
Teacher AI 备课专家:K-12 自动化教案设计 - Openclaw Skills
专利权利要求映射器:生物技术与制药 IP 分析 - Openclaw Skills
生成 Tesla 车身改色膜:用于 3D 显示的 AI 图像生成 - Openclaw Skills
Taiwan MD:面向台湾的 AI 原生开放知识库 - Openclaw Skills
自学习与迭代演进:AI Agent 成长框架 - Openclaw Skills
HIPC Config Manager: 安全的 API 凭据处理器 - Openclaw Skills
AI精选