加密诈骗检测器:实时欺诈预防 - Openclaw Skills
作者:互联网
2026-04-17
什么是 加密诈骗检测器?
加密诈骗检测器是一款为 Openclaw Skills 开发的高级安全插件,旨在保护用户免受不断演变的 Web3 欺诈威胁。通过采用数据库优先的架构,该技能消了标准区块链扫描器常见的延迟和速率限制问题。它对以太坊地址进行深度分析,检查已知的钓鱼签名、蜜罐合约模式以及可疑的交易留言。
与每次查询都依赖实时 API 调用的传统工具不同,此 Openclaw Skills 实现维护了一个后台同步的本地 SQLite 数据库。这确保了用户在验证潜在风险(如拉地毯或庞氏骗局)时能获得即时结果(低于 5 毫秒)。对于任何希望将强大安全检查集成到自动化工作流中的开发者或交易者来说,这是一个至关重要的工具。
下载入口:https://github.com/openclaw/skills/tree/main/skills/princedoss77/crypto-scam-detector
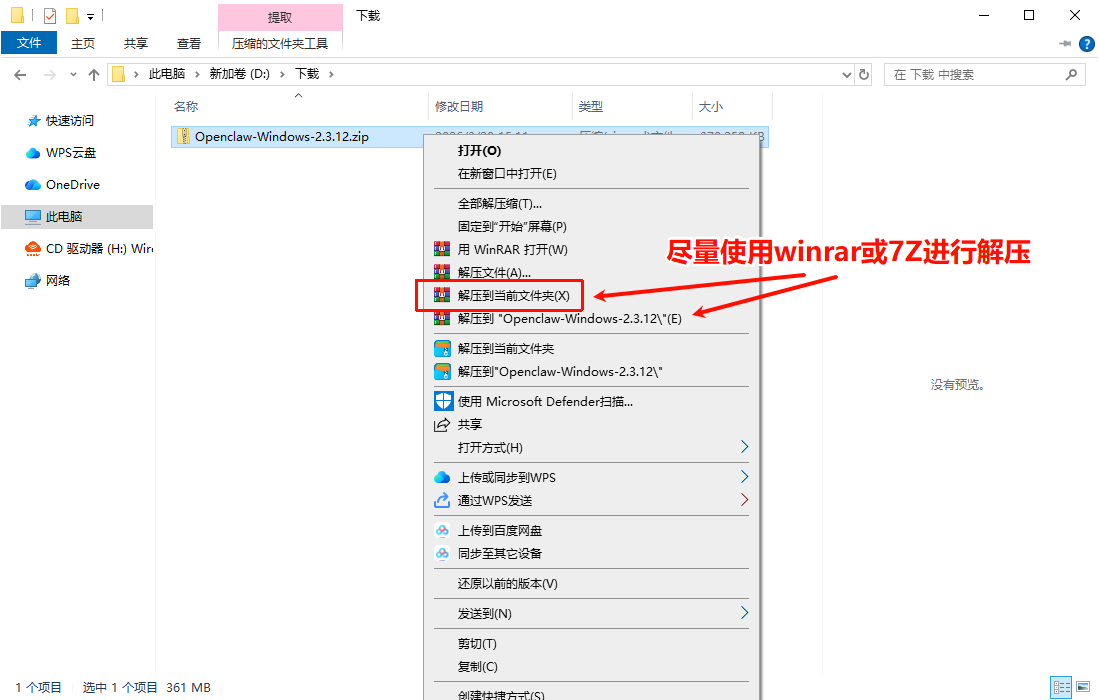
安装与下载
1. ClawHub CLI
从源直接安装技能的最快方式。
npx clawhub@latest install crypto-scam-detector
2. 手动安装
将技能文件夹复制到以下位置之一
全局模式~/.openclaw/skills/
工作区
/skills/ 优先级:工作区 > 本地 > 内置
3. 提示词安装
将此提示词复制到 OpenClaw 即可自动安装。
请帮我使用 Clawhub 安装 crypto-scam-detector。如果尚未安装 Clawhub,请先安装(npm i -g clawhub)。
加密诈骗检测器 应用场景
- 在发送 ETH 或代币前验证目标地址,防止误转账至钓鱼网站。
- 审计智能合约的蜜罐特征或未经验证的代码签名。
- 扫描交易历史,查找与 Lazarus 或 Orbit Bridge 等已知黑客组织的关联。
- 识别隐藏在交易十六进制数据消息中的社交工程陷阱。
- 在 Openclaw Skills 内部维护高风险地址的本地仓库,用于自动化钱包监控。
- 用户通过命令或聊天界面向该技能提供加密货币地址。
- 系统查询本地 SQLite 数据库,获取即时的风险评分和分析报告。
- 如果数据库中存在该地址,用户将收到包含风险等级 (0-100) 和具体诈骗指标的即时报告。
- 如果地址未知,它会自动添加到后台工作程序的优先级同步队列中。
- 后台同步程序从 Etherscan 获取数据,解码交易十六进制数据,并分析关键词以更新数据库供未来查询。
加密诈骗检测器 配置指南
按照以下安装和配置步骤开始使用此 Openclaw Skills 技能:
# 进入您的技能目录
cd ~/.openclaw/workspace/skills/crypto-scam-detector
# 运行自动安装程序
bash install.sh
# 使用加密设置向导配置您的 Etherscan API 密钥
./setup.sh
强烈建议设置定时任务(cron job)以保持本地数据库更新:
# 通过 crontab 每 10 分钟运行一次同步程序
*/10 * * * * cd ~/.openclaw/workspace/skills/crypto-scam-detector && source venv/bin/activate && python3 sync_worker.py --max-jobs 30
加密诈骗检测器 数据架构与分类体系
该技能使用结构化的 SQLite 架构组织其安全情报,以确保在 Openclaw Skills 中实现快速查找和详细报告:
| 表名 | 描述 |
|---|---|
addresses |
存储核心地址元数据、余额信息和最终风险评分。 |
transactions |
存档带有解码十六进制消息的可疑交易,用于深度分析。 |
scam_indicators |
分类列出为每个地址发现的特定红旗指标(例如“钓鱼”、“Lazarus 组织”)。 |
sync_queue |
管理等待完整区块链同步的地址流水线。 |
name: crypto-scam-detector
displayName: Crypto Scam Detector
version: 2.0.0
author: Trust Claw Team
description: Real-time cryptocurrency scam detection with database-first architecture. Protects users from phishing, honeypots, rug pulls, and ponzi schemes. No external API calls during checks!
category: security
tags: [crypto, scam-detection, ethereum, blockchain, security, fraud-prevention, web3, defi, database, etherscan]
license: MIT
repository: https://github.com/trustclaw/crypto-scam-detector
homepage: https://github.com/trustclaw/crypto-scam-detector
icon: ??
command: python3 crypto_check_db.py
?? Crypto Scam Detector v2.0
Database-first cryptocurrency scam detection for OpenClaw
Analyzes crypto addresses for phishing, honeypots, rug pulls, and ponzi schemes using a local database with background sync from Etherscan. Zero external API calls during user checks = instant results!
? What's New in v2.0
?? Major Architecture Upgrade
- ? Database-first design - All checks query local SQLite database
- ? Instant results - No API latency during checks (<5ms)
- ? No rate limits - User queries never hit Etherscan API
- ? Background sync worker - Separate process pulls from Etherscan
- ? Transaction message analysis - Decodes and analyzes hex data
- ? Auto-queue system - Unknown addresses automatically queued for sync
- ? Deep scanning - Detects suspicious keywords in transaction data
?? Enhanced Detection
Now catches scams the old version missed:
- ? "Lazarus Vanguard" hacking group references
- ? "Orbit Bridge Hacker" mentions
- ? Private key phishing attempts
- ? Exploit recruitment messages
- ? And much more...
?? What's Included
crypto-scam-detector/
├── SKILL.md # This file
├── DATABASE_ARCHITECTURE.md # Technical documentation
├── database.py # SQLite database layer
├── crypto_check_db.py # Database-only checker (instant)
├── sync_worker.py # Background Etherscan sync worker
├── secure_key_manager.py # Encrypted API key storage
├── install.sh # Auto-installer
├── setup.sh # API key setup wizard
├── check_address.sh # Convenience script (sync if needed)
├── requirements.txt # Python dependencies
└── venv/ # Virtual environment (created on install)
?? Quick Start
1. Install
cd ~/.openclaw/workspace/skills/crypto-scam-detector
bash install.sh
2. Configure Etherscan API Key (Optional but Recommended)
Option A: Interactive Setup (Encrypted storage)
./setup.sh
# Follow the wizard to encrypt your API key
Option B: Environment Variable
export ETHERSCAN_API_KEY="your_key_here"
Get free API key: https://etherscan.io/myapikey
3. Check an Address
# Check address (instant, database-only)
python3 crypto_check_db.py 0x1234567890abcdef1234567890abcdef12345678
4. Run Background Sync Worker
Manual mode:
python3 sync_worker.py
# Runs continuously, processes queue
Batch mode:
python3 sync_worker.py --max-jobs 20
# Process 20 addresses then exit
Cron schedule (recommended):
# Add to crontab
*/10 * * * * cd ~/.openclaw/workspace/skills/crypto-scam-detector && source venv/bin/activate && ETHERSCAN_API_KEY="key" python3 sync_worker.py --max-jobs 30
?? How It Works
Architecture Flow
User checks address
↓
┌──────────────────┐
│ crypto_check_db │ ← Queries local database ONLY
└────────┬─────────┘ (No external API calls)
│
↓
┌──────────────────────┐
│ Local SQLite DB │
│ ~/.config/crypto- │
│ scam-detector/ │
│ │
│ ? Addresses │
│ ? Transactions │
│ ? Risk scores │
│ ? Scam indicators │
│ ? Sync queue │
└────────▲─────────────┘
│
│ Background sync
│
┌────────┴─────────────┐
│ sync_worker.py │ ← Pulls from Etherscan
│ │ (Uses your API key)
│ ? Reads queue │
│ ? Calls Etherscan │
│ ? Decodes TX data │
│ ? Analyzes messages │
│ ? Stores in DB │
└──────────────────────┘
User Flow
- Check address:
python3 crypto_check_db.py 0x... - If in database: Instant results with full analysis
- If NOT in database:
- Returns "unknown" status
- Automatically adds to sync queue
- Shows: "? Check again in a few minutes"
- Background worker syncs it (next cron run or manual trigger)
- Check again: Full analysis now available
?? Detection Capabilities
Scam Types Detected
| Type | Detection Method |
|---|---|
| Phishing | Keyword analysis: "private key", "seed phrase", "verify wallet" |
| Honeypot | Contract code analysis (unverified contracts) |
| Rug Pull | Transaction pattern analysis |
| Exploit Groups | Keywords: "Lazarus", "hack", "exploit", "breach" |
| Social Engineering | Keywords: "urgent", "claim reward", "airdrop winner" |
Risk Scoring
Algorithm factors:
- Suspicious transaction count (+25 per TX, max +50)
- Account age (new addresses: +10)
- Balance patterns (large balance + suspicious TX: +20)
- Contract verification (unverified: +30)
Risk Levels:
- 0-19: ? Low Risk
- 20-49: ?? Medium Risk
- 50-79: ?? High Risk
- 80-100: ?? Critical Risk
?? Commands Reference
Check Address
# Human-readable output
python3 crypto_check_db.py 0x...
# JSON output
python3 crypto_check_db.py 0x... --json
Sync Worker
# Add address to queue
python3 sync_worker.py --add-address 0x...
# Run worker (continuous)
python3 sync_worker.py
# Process N addresses then stop
python3 sync_worker.py --max-jobs 20
# Custom delay between addresses
python3 sync_worker.py --delay 2.0
# Show database stats
python3 sync_worker.py --stats
Convenience Script
# Check and auto-sync if needed
./check_address.sh 0x...
# Automatically syncs if not in DB, then shows results
?? Example Output
Critical Risk Address
?? Analysis for 0x098b716b8aaf21512996dc57eb0615e2383e2f96
Risk Score: 100/100 - CRITICAL RISK
Last Updated: 2026-02-20 07:14:32
?? KNOWN SCAM DETECTED!
?? Smart Contract
?? NOT VERIFIED on Etherscan
Transactions: 38
Balance: 101.802430 ETH
?? 5 Scam Indicator(s) Detected:
? Suspicious keyword detected: 'lazarus' (confidence: 80%)
? Suspicious keyword detected: 'hack' (confidence: 80%)
? Suspicious keyword detected: 'exploit' (confidence: 80%)
? Suspicious keyword detected: 'private key' (confidence: 80%)
?? 5 Suspicious Transaction(s):
? 0x74f7fbfe5a0bd3...
Reason: Suspicious keyword detected: 'lazarus'
Message: "Greetings Lazarus Vanguard..."
?? Recommendations:
?? DO NOT send funds to this address
?? This address has been flagged as high risk
?? Report the source that gave you this address
Unknown Address (Not Yet Synced)
? Analysis for 0xnew_address_not_in_db
Risk Score: 0/100 - UNKNOWN
Last Updated: N/A
? Address not yet in database
Address not in database. Added to sync queue.
?? Recommendations:
? This address will be analyzed soon
?? Check again in a few minutes
?? Exercise caution until analysis completes
?? Configuration
Database Location
Default: ~/.config/crypto-scam-detector/crypto_data.db
Etherscan API Rate Limits
- Free tier: 5 calls/second, 100,000 calls/day
- Each address: 4 API calls (balance, TX count, TX list, code)
- Default delay: 1.5 seconds between addresses (safe for free tier)
Recommended Cron Schedule
# Every 10 minutes, process 30 addresses
*/10 * * * * cd ~/.openclaw/workspace/skills/crypto-scam-detector && source venv/bin/activate && ETHERSCAN_API_KEY="key" python3 sync_worker.py --max-jobs 30 --delay 2.0
# Handles ~4,320 addresses per day
??? Security
- ? Encrypted API key storage - AES-256 with PBKDF2
- ? No third-party sharing - API key only sent to Etherscan
- ? Local processing - All analysis happens on your machine
- ? No telemetry - Zero data collection
- ? Open source - Fully auditable code
?? Database Schema
Tables
- addresses - Address info, risk scores, balances, metadata
- transactions - Suspicious transactions with decoded messages
- scam_indicators - Individual red flags per address
- sync_queue - Addresses waiting to be synced
See DATABASE_ARCHITECTURE.md for full technical details.
?? Sync Frequency
Default behavior:
- First check → address queued for sync
- Worker processes queue (manual or cron)
- Subsequent checks → instant from database
Recommended: Run worker via cron every 5-10 minutes
?? OpenClaw Integration
Via Chat
"Check if 0x1234... is a scam"
"Is this address safe: 0xabc..."
"Verify 0xdef... before I send ETH"
Automatic Detection
When you check an address, OpenClaw:
- Runs
crypto_check_db.py - If not in DB → queues for sync
- Returns current status
- Suggests checking again after sync
?? Troubleshooting
"Address not in database"
Solution: Wait for background worker to sync it, or manually trigger:
python3 sync_worker.py --add-address 0x...
python3 sync_worker.py --max-jobs 1
"Etherscan API key not configured"
Solution: Set API key via environment or setup wizard:
./setup.sh # or
export ETHERSCAN_API_KEY="your_key"
Rate limit errors
Solution: Increase delay between addresses:
python3 sync_worker.py --delay 3.0
?? Performance
- ? Check latency: <5ms (database query)
- ? Sync time: ~2 seconds per address (4 API calls)
- ? Database size: ~1KB per address
- ? Capacity: Handles millions of addresses
?? Comparison: v1 vs v2
| Feature | v1.1.3 (Old) | v2.0.0 (New) |
|---|---|---|
| Check speed | 2-5 seconds (API calls) | <5ms (database) |
| Rate limits | Yes (every check) | No (checks only query DB) |
| TX message analysis | ? Not analyzed | ? Fully analyzed |
| False negatives | High (missed scams) | Low (deep analysis) |
| Architecture | Direct API calls | Database + background worker |
| API key usage | Every check | Only background worker |
?? License
MIT License - Free and open source
?? Support
- GitHub: https://github.com/trustclaw/crypto-scam-detector
- Issues: Report bugs or request features
- ClawHub: https://clawhub.com/crypto-scam-detector
- Hackathon: NeoClaw Hackathon 2026
?? Credits
Developed by Trust Claw Team for NeoClaw Hackathon 2026
Built with:
- SQLite - Local database
- Etherscan API - Blockchain data
- ChainAbuse API - Community scam reports
- Python asyncio - Async operations
?? Stay safe in crypto! Always verify addresses before sending funds.
相关推荐
专题
+ 收藏
+ 收藏
+ 收藏
+ 收藏
+ 收藏
+ 收藏
最新数据
相关文章
自动化:工作流优化与定时任务 - Openclaw Skills
文本翻译器:免费多语言免 API 翻译 - Openclaw Skills
主管提案者:主动式 AI 代理沟通 - Openclaw 技能
在线状态监控器:网站状态与性能 - Openclaw Skills
Secret Rotator:自动化 API 密钥审计与轮换 - Openclaw Skills
rey-x-api: 为 AI 智能体提供的安全 X API 集成 - Openclaw Skills
Polymarket 交易者:由 AI 驱动的预测市场自动化 - Openclaw Skills
LinkedIn 自动化:扩展 B2B 增长与内容 - Openclaw Skills
Rey 代码审查:自动化质量与安全审计 - Openclaw 技能
Reddit 发布助手:算法优化的社区参与 - Openclaw Skills
AI精选